Ransomware-as-a-Service (RaaS): Why Small Businesses Are the 2026 Target
David Plaha
There is a dangerous misconception that persists in the boardrooms of small businesses: "We are too small to happen." The logic goes: "Why would a Russian hacker waste time encrypting my 20-person accounting firm when they could hack Microsoft?"
In 2015, that logic might have held water. In 2026, it is a fatal error. The landscape of cybercrime has fundamentally shifted. The rise of Ransomware-as-a-Service (RaaS) has industrialized hacking. It has turned cyber espionage into a franchise model, similar to McDonald's.
Today, you aren't being targeted by "state-sponsored spies." You are being targeted by "script kiddies" who rented a powerful weapon for $50 a month. And to them, your small business isn't "small." It's an easy $50,000 payday.
This article explores the mechanics of the RaaS economy, why SMBs are the primary crop for these digital harvesters, and how you can defend yourself against an enemy that is automated, ruthless, and scalable.
1. The Mechanics of RaaS: The "Gig Economy" of Crime
To understand the threat, you must understand the business model. RaaS operates exactly like a legitimate SaaS (Software-as-a-Service) company like Salesforce or Slack. It has hierarchies, customer support, and profit-sharing.
The ecosystem consists of three main players:
A. The Operators (The Developers)
These are the top 1% of cybercriminals. They are brilliant coders and cryptographers.
- Role: They write the ransomware code (e.g., LockBit, BlackCat, Benzona). They build the "payment portal" (where victims go to pay Bitcoin). They manage the cloud infrastructure.
- Risk: They stay deep in the shadows, never engaging with victims directly.
- Income: They take a 20-30% cut of every ransom paid.
B. The Affiliates (The Sales Force)
These are the foot soldiers. They are often low-skilled "script kiddies" or mid-tier hackers.
- Role: Their only job is to break into networks. They don't need to know how to encrypt files; they just need to know how to buy a stolen password or send a phishing email. Once inside, they deploy the Operator's malware.
- Motivation: Volume. They want to hit as many easy targets as possible.
- Income: They keep 70-80% of the ransom. This high commission drives aggressive behavior.
C. Initial Access Brokers (IABs)
The middlemen. They hack networks but don't deploy ransomware. Instead, they sell "access" on the dark web.
- Product: "VPN Access to a US Manufacturing Firm ($5M Revenue) - Price: $500."
- Customer: The Affiliates buy this access to launch their attacks.
2. Why SMBs Are the Primary Target in 2026
The economics of RaaS favor quantity over quality.
The "Volume" Strategy
Attacking a Fortune 500 company is hard. They have multi-million dollar Security Operations Centers (SOCs), 24/7 monitoring, and teams of "Red Hunters." An attack might take 6 months of planning.
Attacking an SMB is easy.
- Low Defense: Many SMBs rely on a basic firewall and free antivirus.
- No Monitoring: No one is watching the logs on Saturday night at 3 AM.
- Speed: An affiliate can breach an SMB, encrypt the servers, and exfiltrate data in under 4 hours.
If an affiliate attacks 100 SMBs and demands $50,000 from each:
- Even if only 10 pay, that is $500,000 in profit.
- This is far easier and safer than trying to extort $5 million from one large corporation.
The Cyber Insurance Factor
Attackers know you have insurance. They often hack the insurance company first to see your policy limits. If they see you have $100,000 in ransomware coverage, guess what the ransom demand will be? $98,000. They make it a "rational business decision" for the insurance carrier to pay rather than fight.
3. The 2026 Shift: Triple Extortion
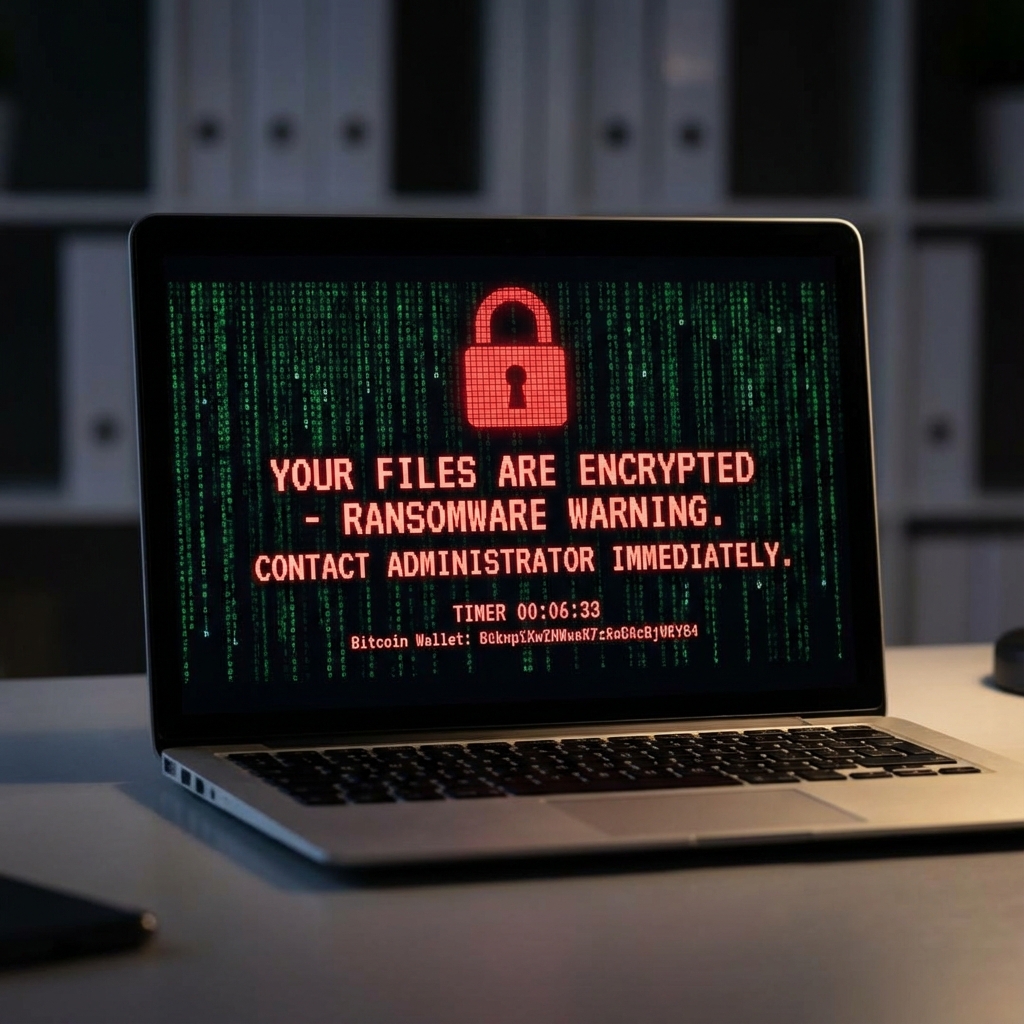
In the old days (2018), ransomware just encrypted your files. If you had backups, you could ignore them. Today, RaaS groups use Triple Extortion:
- Encryption: Your files are locked. Operations stop.
- Exfiltration (Data Theft): Before locking the files, they steal 500GB of sensitive data (client lists, HR records, emails). They threaten to publish this on a "Leak Site" if you don't pay. even if you have backups, you are trapped by GDPR/privacy regulations.
- DDoS: If you still refuse, they launch a Distributed Denial of Service attack against your public website to add pressure.
4. How to Defend Your Business (The Anti-RaaS Playbook)
You do not need an enterprise budget to stop 90% of RaaS attacks. You need Cyber Hygiene.
Phase 1: Close the Front Door (Initial Access)
- Kill Remote Desktop (RDP): Never, ever expose RDP (Port 3389) to the open internet. Access brokers scan the entire internet for open RDP ports every 5 minutes. Use a VPN with MFA.
- Patch Your VPN: High-severity vulnerabilities in VPN gateways (Fortinet, Pulse Secure, Cisco) are the gold standard for easy entry. Patch them within 24 hours of an update.
- Phishing Resistant MFA: SMS-based 2FA is better than nothing, but it can be bypassed. Use FIDO2 hardware keys (YubiKey) or Authenticator Apps.
Phase 2: Detect the intruder (Dwell Time)
Ransomware doesn't detonate instantly. The attacker is usually inside your network for 7-14 days (Dwell Time) moving laterally. This is your window to stop them.
- EDR (Endpoint Detection & Response): Traditional antivirus looks for "known bad files." EDR looks for "bad behavior." (e.g., "Why is PowerShell trying to delete shadow copies?").
- Canary Tokens: Place a fake file named "passwords.xlsx" on your file server. If anyone opens it, you get an email alert. It's a cheap, effective tripwire.
Phase 3: The Safety Net (Resilience)
- Immutable Backups: Ransomware actively hunts for backups to delete them. You need "Immutable" storage (WORM - Write Once Read Many). Even if the hacker gets Admin rights, they cannot delete these backups for a set retention period (e.g., 14 days).
- The 3-2-1 Rule: 3 copies of data, 2 different media, 1 copy OFFLINE. The offline copy is the only one you can trust 100%.
5. Conclusion: The Cost of Inaction
Defending against RaaS is a cost of doing business in 2026. The average cost of downtime for an SMB is $8,000 per hour. The average ransom demand is $150,000. The cost of effective prevention (MFA, EDR, Backups) is a fraction of that.
Do not wait until you see the red skull on your screen. Defend your network today.
Need a vulnerability assessment? Contact Cyberlord to identify the open doors in your network before an Initial Access Broker sells them to the highest bidder.
ransomware as a service smb guide overview
Key decisions, risks, and implementation actions for ransomware as a service smb guide.