Mobile Phone Forensic Examination: The 2025 Guide for Victims & Businesses
CyberLord Forensics Team
Your phone is not just a phone. It is a "Black Box" of your life. It knows where you slept last night (GPS), who you talked to (Call Logs), what you bought (Wallet), and your deepest secrets (Signal/WhatsApp).
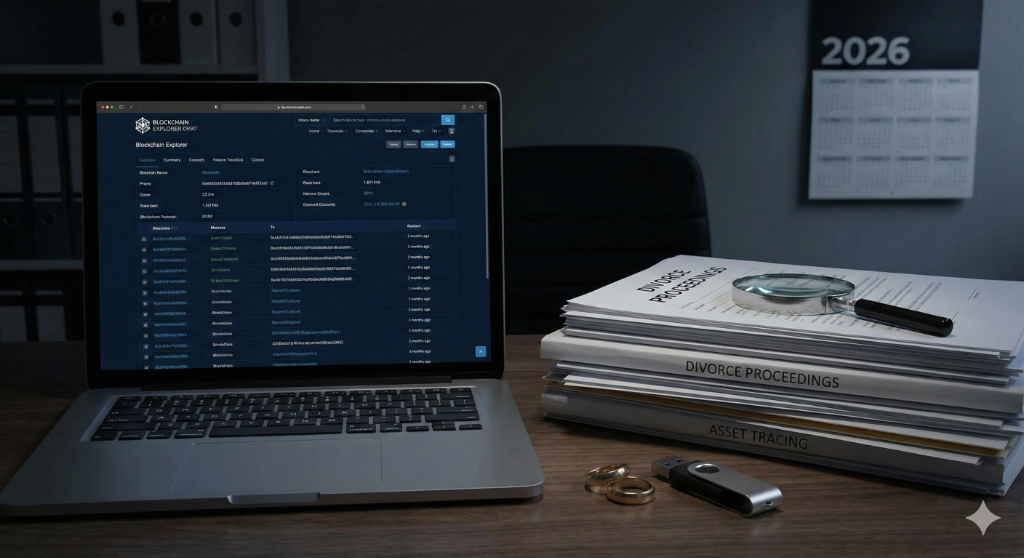
When a security incident occurs—whether it's corporate espionage, a complex divorce case, or a suspicion of state-level spyware like Pegasus—a simple "antivirus scan" is not enough. You need a Mobile Phone Forensic Examination.
In 2025, mobile forensics has evolved from "recovering deleted texts" to "analyzing RAM for ephemeral malware." This definitive guide explains what happens inside a forensic lab, what evidence can actually be recovered from modern iPhones and Androids, and why "Factory Reset" doesn't always hide the truth.
What is a Mobile Forensic Examination?
A forensic examination is a scalable, legally defensible process of identifying, preserving, analyzing, and presenting digital evidence.
Unlike a data recovery service (which just wants to get your photos back), a forensic exam focuses on Integrity:
- Chain of Custody: We document exactly who held the device and when.
- Read-Only Access: We use "Write Blockers" to ensure we don't accidentally modify the data on the phone during the scan.
- Hash Verification: We calculate a digital fingerprint (Hash) of the data before and after extraction to prove in court that the evidence was not tampered with.
The 3 Levels of Data Extraction
Not all forensic exams are created equal. Depending on the device model (iPhone 16 vs. Samsung S25) and the lock state (Passcode known vs. unknown), we use one of three methods:
Level 1: Logical Extraction (The "Backup")
This is similar to an iTunes backup but on steroids.
- What we get: Active files (Photos, SMS, Contacts, Call Logs), App Data (WhatsApp databases).
- What we miss: Deleted data, system logs, hidden partitions.
- Speed: Fast (1-2 hours).
- Use Case: Harassment cases, employee misconduct where the PIN is known.
Level 2: File System Extraction (The "Deep Dive")
We use vulnerabilities in the phone's OS (like Checkm8 for older iPhones) to get "Root" access temporarily.
- What we get: Everything in Level 1 + System Logs (crucial for malware analysis), usage artifacts (Pattern of Life), and some deleted database records (WAL files).
- Use Case: Spyware detection, corporate espionage.
Level 3: Physical Extraction (The "Bit-by-Bit")
We create a clone of the phone's flash memory chip.
- What we get: Everything. Deleted files that haven't been overwritten, fragments of unallocated space.
- Limitation: Extremely difficult on modern phones due to Full Disk Encryption (FDE). On an iPhone 15/16, this is virtually impossible without the passcode. On older Androids, it is standard practice.
Detecting Modern Spyware (Pegasus, Predator, Reign)
In 2025, you aren't looking for an app called "Virus.exe." State-sponsored spyware like Pegasus is "fileless." It lives in the phone's memory or mimics system processes.
During a forensic exam, we look for IoCs (Indicators of Compromise) that valid users never see:
- Anomalous Processes: Why is the "Calculator" app sending 50MB of data to a server in Bulgaria at 3 AM?
- Battery Usage: Spyware drains power. A sudden drop in battery health often correlates with infection.
- System Inconsistencies: If an iPhone says it hasn't been rebooted in 30 days, but the system logs show a kernel panic happened yesterday, that "panic" might have been the exploit crashing the phone to gain persistence.
Note: Detecting Pegasus requires a Level 2 (File System) extraction. You cannot detect it with a simple app store scanner.
What Evidence Can Be Recovered? (Real World Examples)
1. "Deleted" WhatsApp & Signal
When you delete a message in WhatsApp, it isn't erased immediately. It is marked as "free space."
- Forensic Reality: If we act fast, we can often recover these messages from the SQLite Write-Ahead Logs (WAL).
- Signal: Signal encrypts its database heavily. However, if we have the passcode, we can decrypt the database and see the messages. Disappearing messages are harder, but sometimes recoverable from "notification caches."
2. Location History (Significant Locations)
Your iPhone tracks your "Significant Locations" (Home, Work, Frequent Visits) to optimize traffic routing.
- Forensic Reality: We can extract this map. We can prove the suspect was at the Crime Scene at 9:00 PM, even if they turned off Google Maps.
3. "Pattern of Life"
We build a timeline of the user's habits.
- When was the phone locked/unlocked?
- When was it plugged into a charger?
- When did the pedometer register steps?
- Example: In a murder case, the suspect claimed to be sleeping at 11 PM. The forensic exam showed the phone's pedometer registered 2,000 steps between 11:00 and 11:30 PM. The alibi collapsed.
FAQ: Common Questions from Clients
Q: Can you unlock a locked iPhone? A: It depends. For older iPhones (iPhone X and below), yes, using GrayKey or Cellebrite. For modern iPhones (13, 14, 15+), it is extremely difficult without the passcode. Brute-forcing a 6-digit code takes forever due to Apple's "Secure Enclave" delays. If the code is alphanumeric, it is mathematically impossible in a human lifetime.
Q: Does a Factory Reset destroy evidence? A: On modern smartphones with encryption: Yes. A factory reset deletes the "Encryption Key." Without the key, the data is just random noise. Recovery is impossible. However, we can sometimes find cloud backups (iCloud, Google Drive) that were created before the reset.
Q: Is this process legal? A: We only conduct examinations if:
- You own the device.
- You have a court order / warrant.
- It is a corporate device, and company policy states "No expectation of privacy." We do not hack spouses' phones for jealous partners. That is illegal.
Summary: Do You Need an Exam?
If you suspect your digital life has been compromised, do not guess. Preserve the evidence.
- Put the phone in Airplane Mode (to stop remote wiping).
- Put it in a Faraday Bag (to block signals).
- Do not turn it off (modern encryption is harder to break after a reboot - BFU mode).
- Contact a forensic expert immediately.
At Cyberlord, our Mobile Forensics Unit uses the same tools as the FBI (Cellebrite, Oxygen, Magnet) to uncover the truth buried in the silicon.
mobile phone forensic examination 2025 guide overview
Key decisions, risks, and implementation actions for mobile phone forensic examination 2025 guide.